Reading this paper just blew my mind – and I’m still not sure I fully understand it. As a matter of fact, I think only a handful of people worldwide can understand exactly how something like this works – but I’ll do my best to explain.
Most computers (especially laptops) emit a high-pitched noise during operation, due to vibration in their electronic components. But this noise doesn’t exist just to annoy you and tell you the computer is actually working – researchers have shown that the sounds can actually give information about the software running on the computer, and in particular leak sensitive information about security-related computations. But the information is not just limited to software – researchers have now shown that different RSA keys induce different sound patterns, that information can be used.
‘But what’s an RSA key?‘, you might ask. Well, that’s a good, and fairly complicated question. RSA is a cryptosystem, which is known as one of the first practicable public-key cryptosystems and is widely used for secure data transmission. In such a cryptosystem, the encryption key is public and differs from the decryption key which is kept secret. RSA algorithm has a very widespread usage throughout the entire world. Oh, and if you’re wondering what RSA stands for, it’s just the name of its inventors: Ron Rivest, Adi Shamir and Leonard Adleman.
Each time you login in, with your password, the RSA algorithm will generate, encrypt, and then decrypt a key.
So what information can be leaked?
In most PCs, it was possible to distinguish most of the programs which the computer was running, and in some of them it was possible to distinguish between the acoustic signature of different RSA secret keys (signing or decryption), and fully extract decryption keys, by measuring the sound the machine makes during decryption of chosen ciphertexts.
You don’t need any special equipment, although that certainly helps. All you need is a mobile phone placed at 20-30 cm from the computer you want to hack.
A possible hack situation
The researchers present just a situation in which this kind of technology could be used:
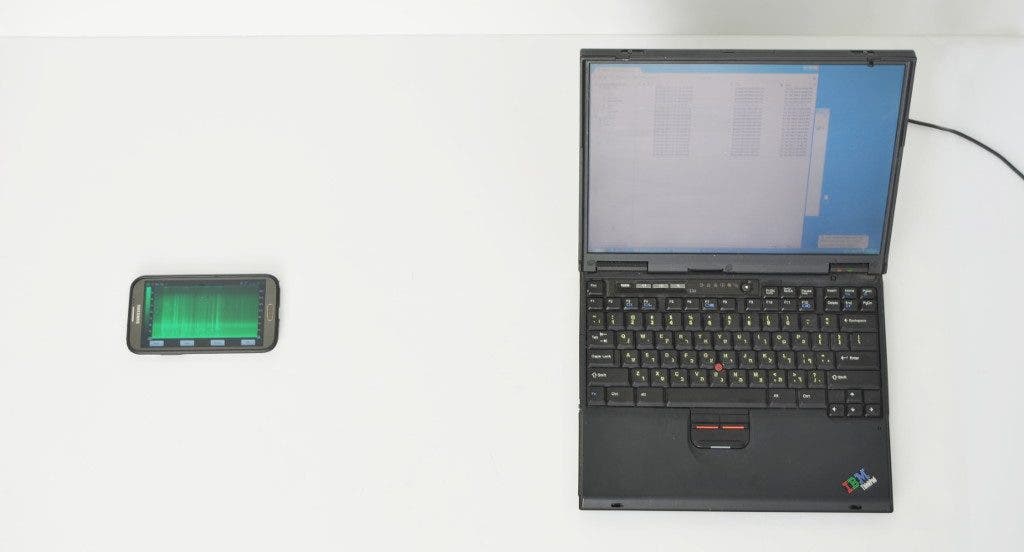
Install an attack app on your phone. Set up a meeting with your victim, and during the meeting, place your phone on the desk next to the the victim’s laptop (see Q2).
Break into your victim’s phone, install your attack app, and wait until the victim inadvertently places his phone next to the target laptop.
Have a web page use the microphone of the the computer running the browser (using Flash or HTML Media Capture). Use that to steal the user’s GnuPG key.
Put your stash of eavesdropping bugs and laser microphones to a new use.
Send your server to a colocation facility, with a good microphone inside the box. Then acoustically extract keys from all nearby servers.
Get near a TEMPEST/1-92 protected machine, such as the one pictured to the right. Put your microphone next to its ventilation holes and extract its supposedly-protected secrets.
The author of this paper, which you can read in its entirety here is Adi Shamir, one of the inventors of the RSA.